NIST 800-171 and CMMC Compliance in M365
A Consolidated Source for Application of NIST 800-171 and CMMC 2.0 to the M365 Platform
This guide is intended to help you identify the NIST 800-171 requirements needed for a successful CMMC implementation using Microsoft products.
In addition, the following content will better prepare your company for a Cybersecurity Maturity Model Certification (CMMC) assessment.
This primer explains requirements, including CMMC Domains and NIST control families, to help businesses identify what is needed for handling Controlled Unclassified Information (CUI) content in your IT systems.
Topics Covered
- What is NIST?
- How Does NIST 800-171 Impact Contractors and CMMC?
- What is CUI?
- What is an SSP and POA&M and Why is it Important?
- Preparing for CMMC Assessments
What is NIST 800-171 and how does it relate to CMMC?
The National Institute of Standards and Technology is the United States agency tasked to advance measurement science, standards and technology in ways that enhance the economic security and improve quality of life.
Federal Information Security Modernization Act (FISMA) established NIST as the responsible agency for development of information security standards and guidelines for federal information systems.
NIST published Special Publication 800-171 titled “Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations” or NIST 800-171 for short.
NIST based 800-171 on 800-53, but removed controls, or parts of controls, that were uniquely catered to federal organizations. The framework consists of 14 Control Families, whereas CMMC contains 17 Domains.
NIST 800-171 is a guideline for non-federal organizations that must securely process CUI content, within internal and external information systems, in support of federal activities.
For Government Contractors supporting the Department of Defense (DoD), CMMC 2.0 Level 2 and DFARS 7012 require NIST 800-171 compliance across information systems and policies.
How Does NIST 800-171 Impact Contractors and CMMC 2.0?
CMMC compliance is mandatory for all DoD contractors and subcontractors who handle CUI. By adhering to the controls outlined in NIST SP 800-171 and obtaining third-party certification of its implementation, organizations can achieve CMMC compliance.
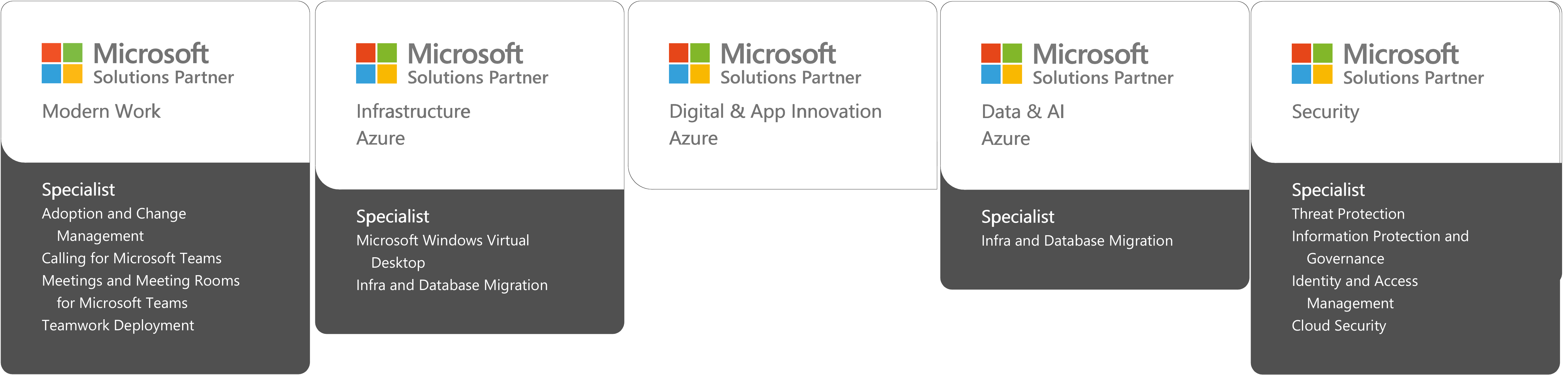
Depending upon your business' previous investments and current security posture, it may be cost-effective to implement security solutions that satisfy NIST 800-171 by using Cloud Solution Providers (CSP) and other cloud services, as long as they are FedRAMP authorized at a moderate baseline or higher, or FedRAMP equivelent as stringently defined by the December 2024 Memo. Improving security with a CSP like Microsoft and leveraging their Office 365 (O365) / Microsoft 365 (M365) collaboration stack may more affordably meet your organizational requirements. Alternatively, but equally effective, security measures may compensate for the inability to satisfy a particular requirement within NIST 800-171. NIST 800-53 provides recognized alternative security standards as organizations plan for NIST 800-171 compliance.
Read more about CMMC 2.0 compliance here.
What is CUI?
Controlled Unclassified Information (CUI) and Covered Defense Information (CDI) are relatively new markings, but similar markings have a long history within the government. CDI is an umbrella term that encompasses all CUI and Controlled Technical Information (CTI). These three markings are given to unclassified content that must be protected in a very specific manner both within and outside a government information system. In the past, the government used many different markings to identify this kind of information. You may have seen or used some of these in the past: Unclassified Controlled Technical Information (UCTI), Sensitive but Unclassified (SBU), For Official Use Only (FOUO), Law Enforcement Sensitive (LES), etc. These are now all rolled up into the classification of CDI content. Clear as mud…. Right? No one said this was easy….
CDI as a category encompasses both CTI and CUI. CTI is defined as technical information with a military or space application that is marked with a distribution statement in accordance with DoDI 530.24 (Distribution Statements on Technical Documents). In general, the controlling Department of Defense (DoD) office is responsible for determining if the information is CTI and properly marking it prior to contractor access to the information. However, if a contractor develops unclassified CTI in the performance of a contract, the contractor must work with the contracting officer to ensure that the appropriate forms are completed, statements of work are in place and distribution statements are assigned to each piece of content. This content must be protected at the same level as other CDI and CUI content; it just has special marking and tracking requirements.
Click Here for a Full Overview of CUI, CDI, CTI, and More
What is an SSP and POA&M?
For starters, a System Security Plan (SSP) is an iterative document meant for updates as the company changes anything substantive about its security posture. Much like a well-kept Wikipedia page, every major update or remediation needs to be recorded and reviewed by other individuals. Information like network diagrams, administration roles, company policies, and security responsibilities by employee type are important for a complete SSP.
For the purposes of NIST 800-171 and CUI requirements, the SSP includes the necessary information about each system in your environment that processes, stores, and transmits CUI. This information includes security configurations or capabilities that are currently or intended to be implemented, and each capability is expressly tied to specific security requirements and controls. Furthermore, the SSP defines how each of these systems interact with one another (flow of information and shared authentication/authorization), as well as how they behave separately.
If the SSP is the collective details of a business' security posture and system(s) profile, the POA&M is the honey-do list. Each company's POA&M is likely different because it includes information about weaknesses and gaps according to NIST 800-171 standards, as well as the risk posture for each respective gap and any mitigating steps the company intends to make. We often suggest similar entries into each of our clients' POA&M's; however, not every company will decide to address every risk in the same way. After all, these are business decisions with operational and financial implications.
Bottom line: you have to possess a complete SSP and POA&M in order to conduct work for the Federal Government. A "complete" SSP is a working and living document nevertheless, and a "complete" POA&M really is an empty document once you configure Office 365 and your other systems properly.
Although NIST 800-171 did require organizations to have a POA&M, CMMC is not going to require contractors to have a POA&M; a SSP will be required. The benchmark of CMMC is 100% compliance: a perfect SPRS score is required to receive a certification. Actually, a POA&M is not going to be allowed with CMMC Level 1. For Levels 2-3, only 1/3 of the controls will allow for POA&Ms, but must be cleared within 180 days, and must be maintained perfectly after (see section 170.21 of the CMMC proposed rule for restrictions).
NIST 800-171 Requirements and Control Families and CMMC Domains
NIST 800-171 is a comprehensive set of requirements containing 28 basic security requirements and 81 derived security requirements. That’s a total of 110 requirements across the entire scope of NIST SP 800-171! CMMC contains 17 Domains and 171 Practices.
Many of these controls or practices can be technical and/or procedural. Some of them are handled by your Cloud Service Provider if you are moving into a Cloud environment.
Preparing for CMMC and DFARS Compliance Audits
Audits of any kind have the potential for varying interpretations by different auditors, and CMMC looks to remedy this through an open and explicit process. A good place to start your understanding, if you have an Microsoft 365 tenant, take a look at this overview of CMMC 2.0 Level 2 requirements.
Small businesses should “Prepare Early and Test Often”. If CMMC and DFARS compliance is an essential element of your business success then be sure to do it right the first time. If you do it incorrectly, you will only end up doing the work a second or third time and small businesses can’t afford to pay for the same work three different times.
For most contractors that have some semblance of an SSP and POA&M, the business will likely need a gap analysis to identify what steps are needed to bring their existing O365 environment to a compliant state OR they will need to configure their new O365 environment to NIST 800-171 prior to migration.
M365 GCC High can be configured to presently slated CMMC standards, with appropriate licensing, and be NIST 800-171 compliant. Additionally, Microsoft agrees to support all requirements for DFARS as part of this environment. This environment was previously available only through an enterprise agreement, requiring 500 or more licenses. Through the AOS-G program, however, it is now available to all organizations with a requirement to manage CUI/ITAR data or have a DFARS 7012 clause in one of their contracts.
Contact Us About NIST and CMMC Compliance
2 Parade St NW
Huntsville, AL 35806
256.585.6868
info@summit7.us
cmmc@summit7.us