Prepare and Document for a CMMC Assessment
Documentation will be what CMMC assesors review to make sure that you are meeting the requirements that your organization has stated it is meeting. This blog covers how to prepare for upcoming CMMC assessments.
Prepare & Document for a CMMC Assessment
Preparing and documenting for a CMMC assessment can be the Achilles heel for aerospace and defense contractors in their CMMC compliance journey as well as the service providers that support them. Documentation will be what Cyber AB C3PAOs (CMMC assessors) review to validate the requirements that your organization has stated it is meeting. Failing to properly map CMMC documentation to the correct standards could result in a failed assessment and the loss of contracts for organizations in the Defense Industrial Base (DIB).
This blog is intended to help you prepare and document for a CMMC assessment. Up to this point in your compliance journey, you should have already done the following steps:
- Established your organization's level of CMMC
- Identified appropriate assets in your organization
- Chosen a technical design for CMMC
- Implemented and or migrated to Microsoft Government Cloud
- Chosen the right Managed Service Provider for your journey
Let's talk about preparing and documenting for a CMMC assessment: Here are the two most common problems we see in improper documentation for CMMC:
- Companies don’t believe that documentation is essential because policies and procedures are not explicitly specified in the practices
- Organizations will solely look at the CMMC requirements (practices) and not the assessment objectives listed in NIST 800-171A (110 controls vs. 320 controls)
This blog is going to cover how contractors can properly prepare and document for CMMC compliance by:
-
Incorporating CMMC / NIST 800-171A into the System Security Plan (SSP)
-
Updating infrastructure maps and data flow diagrams
-
Generating asset inventory lists by category for CMMC Level 2
-
Ensuring your self-assessment report and POA&M are completed for review
-
Defining organizational responsibilities vs. your service provider
-
Gathering FIPS 140-2 validated URLs and screenshots
Incorporating CMMC / NIST 800-171A into the SSP
Thoroughly incorporating CMMC Level 2 (NIST 800-171A) into the SSP (System Security Plan) for the affected scope and mapping policies and procedures accordingly is crucial in proper prep and documentation; this is the most important document that will be reviewed during an assessment.
An example of the SSP can be found on the NIST website (picture below) and is detailed for each Controlled Unclassified Information (CUI) asset that would be impacted by each practice and assessment objective. The detail necessary to demonstrate valid implementation of each practice cannot be underestimated: the more thorough the SSP, the more likely it will be that the assessor understands the maturity of the organization’s security program.
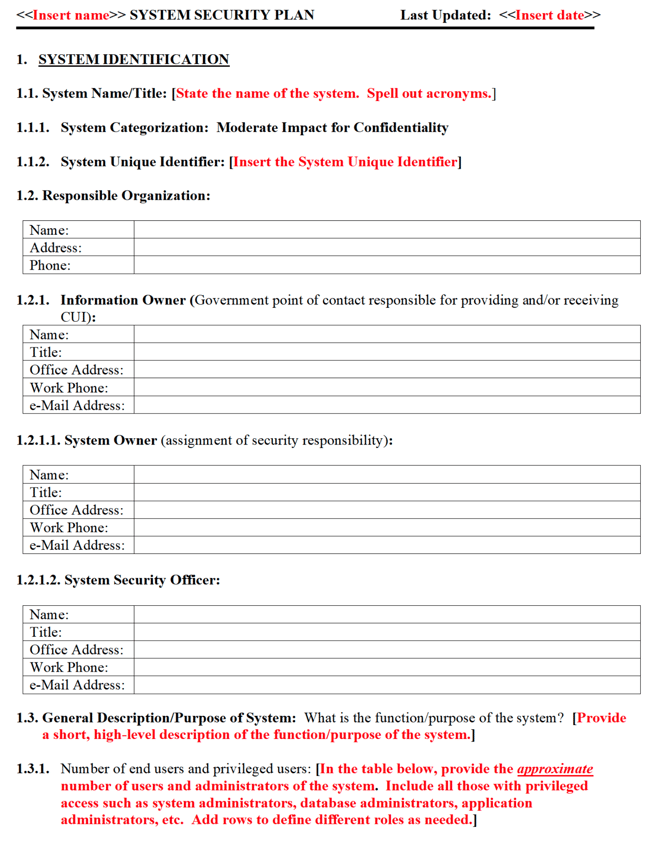
Note that you could potentially have several SSPs. For example, there may be an SSP for the overall organization that addresses all resources (people, assets, facilities), and a separate SSP to cover an enclave for CUI data.
The scope of the assessment will need to be carefully planned and documented as your organization will likely need to address scrutiny of the boundaries, people, and assets that are included. Reference the Step 2: Identifying Assets for CMMC blog to understand the asset categories and how they differ from CMMC Assessment Scope Level 1. CMMC Level 2 has additional categories included in the scope, such as the CRMA or Contractor Risk Managed Asset.
One example of a CRMA could be a desktop or laptop that is used to access a virtual desktop environment such as Azure Virtual Desktop. These assets are very capable of processing, storing, and transmitting CUI, but are not intended to. You would need to ensure there are restrictions in place by policy, procedures, and practices that prevent the device from handling CUI. This can easily be accomplished by having a user policy in place that prohibits copying, printing, or otherwise transferring CUI to the device. However, the best practice (and the recommended method) would be to configure the VDI environment in such a way that these actions are prohibited by technical controls/settings. If you have documented and can show evidence of these controls in place, the assets used to access the VDI environment should be considered Contractor Risk Managed Assets.
Updating Infrastructure Maps and Data Flow Diagrams
Updating the infrastructure map(s) and data flow diagram(s) to reflect the scope of the assessment is a worthwhile, and necessary endeavor for companies to properly prepare for CMMC. The infrastructure map should reflect all devices and network subnets within the scope boundary, demonstrating where and how external connections are included. An Organizational Chart of the people who are in scope, as well as a Data Flow Diagram representing how the people and systems interact with the CUI, is also recommended.
Generating Asset Inventory Lists By Category For CMMC Level 2
It's important that you understand how to generate the asset inventory lists for each category of CMMC Level 2 assets. The SSP will reference the above items and will likely reference asset inventory lists which can be included as appendix items. It is also important to consider whether certain systems, devices, or users who are being removed from the scope (I.e. “Not in Scope”) should be listed as well to better illustrate how and why they are not in scope.
An example might be test equipment that is separated from the network via DMZ or separate physical cabling, that an assessor may see is physically located in the same area as CUI equipment.
Ensuring Your Self-Assessment Report and POA&M Are Completed for Review
A potentially overlooked item, and often misunderstood duo: making sure that your most recent self-assessment report along with the corresponding POA&M items showing completion or activity is ready for review. An item included in the public draft version of the CMMC Assessment Process (CAP) v1.0, which may be required for review in the readiness phase, is the most recent self-assessment on the same assets under NIST 800-171A. Although this item may be removed from the CAP as a required document for an assessor to review in the readiness phase, it would make sense that having a recent self-assessment report along with the results aligned to risk, and how the risks were addressed; for example, closed-out items on a Plan Of Action and Milestones, or POA&M, would reflect the implementation of CA.L2-3.12.1 Security Control Assessment.
Defining Organizational Responsibilities vs. Your Service Provider
Defining the responsibilities of your organization vs. those of your service providers with an SRM (Shared Responsibility Matrix) along with applicable FedRAMP packages can make or break companies in their CMMC preparation. As discussed in Step 5: Find a MSP for CMMC, any external service provider who is responsible for the security of your systems that process, store or handle CUI – even if that provider does not directly process, store or handle CUI themselves, will become part of your CMMC Level 2 assessment. Accordingly, their documentation on how they implement the affected controls will need to be ready, including the SRM (Shared Responsibility Matrix) for those controls. The service provider should partner with your organization to be ready for their role in the CMMC Level 2 assessment.
Additionally, if that service provider directly processes, stores or handles CUI, they may be required to demonstrate FedRAMP moderate or equivalent security maturity themselves. This involves not just the SRM for the affected assets and practices, but you will need to have their FedRAMP package ready for assessor review.
Gathering FIPS 140-2 Validated URLs and Screenshots
Finally, a piece of documentation that your organization will need to have ready, and one that many companies miss, is the FIPS 140-2 validation for any encryption-related assets or systems. This is required of the organization by CMMC 2.0 level 2 practices: SC.L2-3.13.8: Data in Transit, SC.L2-3.13.11: CUI Encryption, AC.L2-3.1.19: Encrypt CUI on Mobile, MP.L2-3.8.6: Portable Storage Encryption, and SC.L2-3.13.16: Data at Rest. Gathering FIPS 140-2 validated URLs and screenshots for affected systems, software, and devices is an often overlooked, but critical step in the preparation and documentation for a CMMC assessment.
Conclusion
This list is not meant to be exhaustive for any type of documentation, as each organization will have different scopes, a number of sites, and many other caveats. Your organization should seek the assistance of skilled consultants when you’ve deemed that your company is well prepared. Seeking a Readiness Assessment from an authorized Cyber AB C3PAO will confirm whether your documentation efforts are complete, before starting on the formal CMMC Level 2 assessment.
Subscribe to the blog and the Summit 7 YouTube channel to get notified of the final step in the 7 Steps to CMMC series. Also, be sure to check out the 7 Steps to CMMC page where we break down each step into digestible blogs and videos.




.jpg)
