How to Get an Exception for NIST 800-171
Only the DoD CIO decides whether a NIST SP 800-171 requirement can remain unimplemented.
Turns out you can get an exception for NIST 800-171 requirements that might be Non-Applicable in your organization's case. But who decides if NIST SP 800-171 Requirements are Non-Applicable?
If you find yourself implementing NIST 800-171 controls for your organization's overall compliance posture, there are likely some technicalities and questions you will have regarding which controls are relevant and/or applicable to your specific organization. You should make sure you seek clarification from the Department of Defense (DoD) and always know your contractual obligations under DFARS 7012. This blog will aid in determining if a NIST SP 800-171 requirement can remain un-implemented, how to submit a formal exception to the DoD CIO and how to properly document it for an assessment.
Key Takeaways:
- There are two situations in which a NIST SP 800-171 requirement can remain un-implemented.
- Only the DoD CIO decides whether a NIST SP 800-171 requirement is either not applicable or if an alternative implementation provides adequate security in-place of a specific NIST requirement.
- In the case of alternative implementations, contractors must explain how their alternatives are equivalent.
- Utilizing your System Security Plan (SSP) to properly document your approved NIST exception for future assessments.
Who Decides?
According to the DoD there are two situations in which a NIST SP 800-171 requirement can remain un-implemented. First, if an alternative security measure has deployed instead of a specific NIST SP 800-171 requirement. Second, if the SP 800-171 requirement is “not applicable”.
The basis for determining if an alternative to a security requirement is acceptable is whether the alternative is equally effective; the basis for determining a security requirement is “not applicable” is whether the basis or condition for the requirement is absent.
However, only the DoD CIO decides whether a NIST SP 800-171 requirement is either not applicable or if an alternative implementation provides adequate security in-place of a specific NIST requirement.

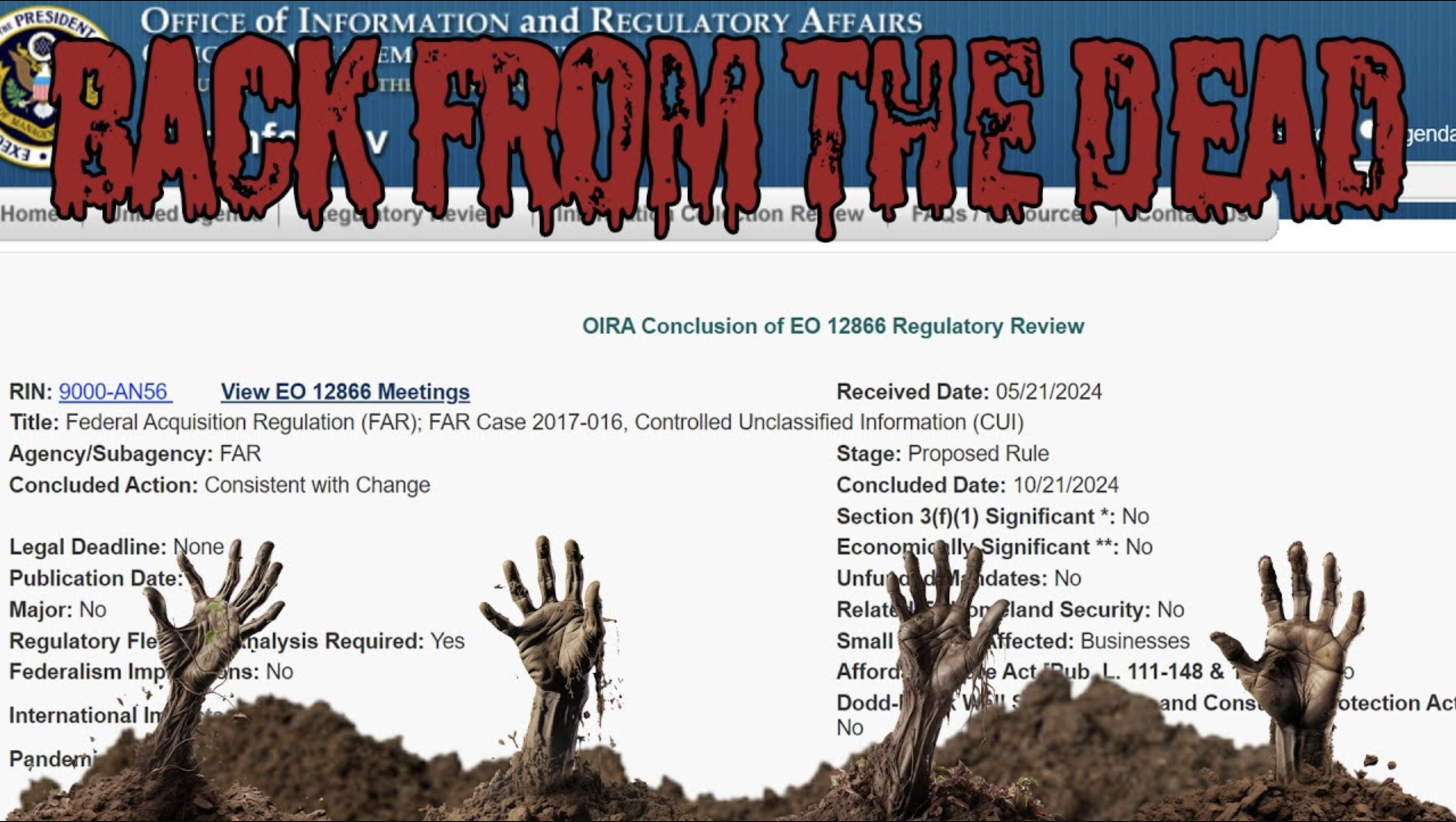
The contract clause DFARS 252.204-7012 was revised in 2016 to expand the obligations of defense contractors to report cybersecurity incidents involving Controlled Unclassified Information (CUI). However, one of the lesser known changes was to:
Clarify that contractors are not required to implement any security requirement if an authorized representative of the DoD Chief Information Officer (CIO) has adjudicated the contractor's request to vary from NIST SP 800-171 and indicated the security requirement to be nonapplicable or to have an alternative, but equally effective, security measure
As part of the same rulemaking in 2016, the DoD created the contract provision DFARS 252.204-7008 to ensure:
…that offerors are aware of the safeguarding requirements of DFARS clause 252.204-7012 and provides a process for the offeror to identify situations in which a security requirement in NIST SP 800-171 is not necessary in performance of the contract, or to propose an alternative to a security requirement is NIST SP 800-171.
Whether contractors are seeking adjudication from DoD CIO in response to the DFARS provision or clause, the DoD explains,
In such cases, the offeror must provide a written explanation in their proposal describing the reasons why a security requirement is not applicable, or how alternative, but equally effective, security measures can compensate for the inability to satisfy a particular requirement. The contracting officer will refer the proposed variance to the DoD CIO for adjudication. The DoD CIO is responsible for ensuring consistent adjudication of proposed non-applicable or alternative security measures. If the DoD CIO needs additional information, a request is made to the contracting officer. Responses are then returned to the contracting officer who, in turn, advises the contractor of the decision. The timeframe for response by the DoD CIO is typically within five business days.
How Do Defense Contractors Contact DoD CIO?
Buried in the contract clause DFARS 252.204-7012 is an email address for the office of the DoD CIO: osd.dibcsia@mail.mil
According to DFARS clause 252.204-7012,
The Contractor shall submit requests to vary from NIST SP 800-171 in writing to the Contracting Officer, for consideration by the DoD CIO. The Contractor need not implement any security requirement adjudicated by an authorized representative of the DoD CIO to be nonapplicable or to have an alternative, but equally effective, security measure that may be implemented in its place.
More details are provided in DFARS provision 252.204-7008. For requests to vary from SP 800-171 based on non-applicability, contractors must explain why a requirement is not applicable. In the case of alternative implementations, contractors must explain how their alternatives are equivalent.
If the Offeror proposes to vary from any of the security requirements specified by NIST SP 800-171 that are in effect at the time the solicitation is issued or as authorized by the Contracting Officer, the Offeror shall submit to the Contracting Officer, for consideration by the DoD Chief Information Officer (CIO), a written explanation of—
(A) Why a particular security requirement is not applicable; or
(B) How an alternative but equally effective, security measure is used to compensate for the inability to satisfy a particular requirement and achieve equivalent protection.
(ii) An authorized representative of the DoD CIO will adjudicate offeror requests to vary from NIST SP 800-171 requirements in writing prior to contract award. Any accepted variance from NIST SP 800-171 shall be incorporated into the resulting contract.
Is it the Same Process for Defense Subcontractors?
Yes. In the same way that DFARS clauses “flow down” to subcontractors and obligate them to implement NIST SP 800-171 requirements, the requirement to properly engage with DoD to request non-applicability and/or alternative implementations also flows down.
DFARS clause 252.204-7012 is amended by adding a new paragraph (b)(2)(ii)(B) to clarify that the contractor may request the contracting officer seek DoD CIO adjudication on variances from NIST SP 800-171 requirements after award. DFARS clause 252.204-7012 is flowed down to subcontractors without alteration when performance will involve operationally critical support or covered defense information. However, paragraph (m) of the clause is amended to clarify that the prime contractor shall require subcontractors to notify the prime contractor (or next higher-tier subcontractor) of any requests for variance submitted directly to the contracting officer.
Is DoD CIO Approval Always Required?
The DoD Procurement Toolbox hosts a collection of 136 Cybersecurity FAQs related to NIST SP 800-171 requirements, including the process for requesting to vary from the requirements or use alternative controls (Questions 62 – 66). Note: even though the DoD Procurement Toolbox has a “.com” top-level domain, it is an official website of Defense Pricing and Contracting within the Office of the Secretary of Defense.
Most of the answers are simply word-for-word restatements of DoD policy established in and explained by rulemaking. However, question 65 can be somewhat confusing.
Q65: Are there circumstances when DoD CIO adjudication of ‘Alternative’ or ‘Not Applicable’ solutions is not required?
A65: Yes, when the contractor’s policy, process, etc., does not allow the circumstances addressed in the NIST SP 800-171, the contractor need only document the details surrounding the situation in the system security plan per NIST SP 800-171 (Chapter 3) and DFARS clause 252.204-7012 (b)(3).
If the functionality addressed by the requirement is not permitted (e.g., 3.1.14, Route remote access via managed access control points), and the organization has a policy and procedure in place (and documented in the system security plan required by 3.12.4) to enforce the prohibition, then no approval of 'non-applicability' is required as the requirement is considered to have been implemented.
In addition, in situations where specialized systems, such as medical devices, CNC or other shop floor equipment, cannot by their nature meet the NIST SP 800-171 requirements, there is no need to request approval for an alternative or not applicable solution. These situations should be addressed in the contractor’s system security plan.
Summary
As it stands this is the official method for obtaining DoD concurrence and approval for control variations, deviations, and/or non-applicability exists within DFARS contract clauses and provisions. Yet, DoD’s cybersecurity FAQs suggest that contractors can unilaterally make that decision themselves. While this is great for flexibility, it can lead to problems during a DIBCAC, Join Surveillance, or CMMC assessment.
Ultimately, the question comes down to this: during an assessment would you rather point to the FAQ #65 or an official approval directly from DoD CIO?